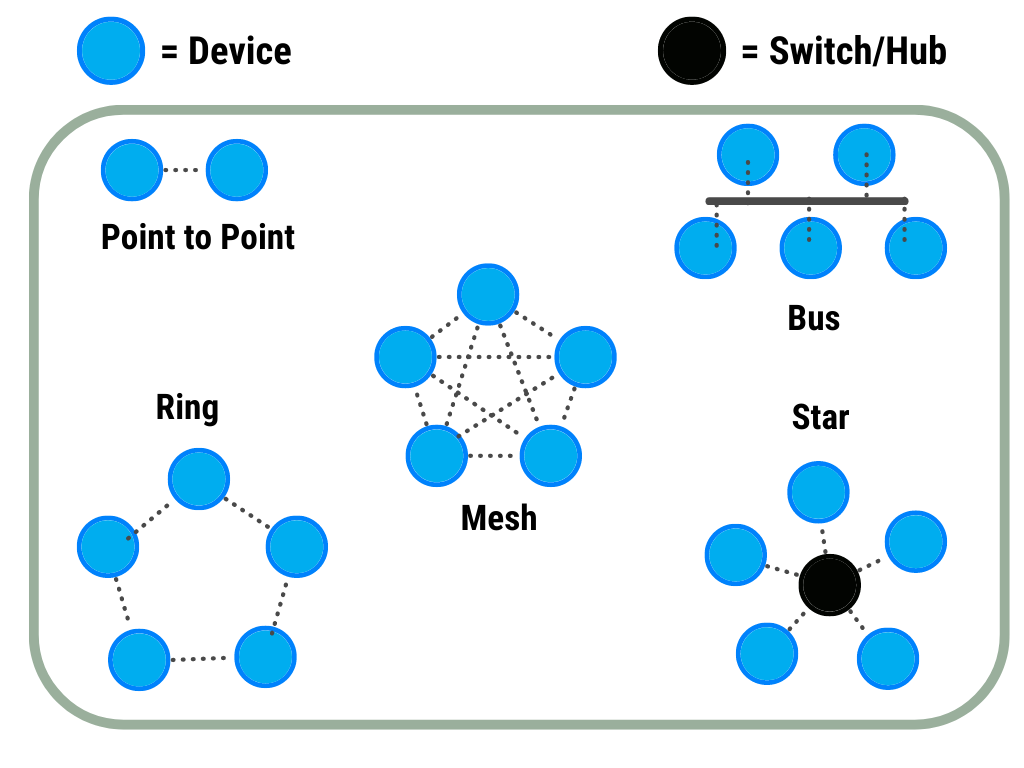
Network topology is a term for how electronic devices are connected to each other. It allows us to define the layout of cables, devices, and routing paths in a network. If we think about it from the perspective of the Internet of Things (IoT), it is defined as the communication of sensors, actuators, and gateways with each other. Some common topologies are invaluable for IoT. In this article, we will discuss these common topologies.
Point-to-Point Network (PPP):
It is possible for two points to communicate directly over PPP, which is one of the data link layer protocols. Thanks to this protocol, user control, data compression, and encrypted communication are possible. The PPP protocol is used in many areas, such as telephone communication, fiber optic cable media, radio communication media, and mobile phones. A Bluetooth connection between a mobile phone and a headset is an example of this topology.
Advantages
- Easy to configure and implement
- Less complex than other types of connections
- It is low cost
Disadvantages
- Provides decentralized management
- Efficiency drops as the network grows
Bus:
It is a network topology in which devices are connected to each other with a single cable. This cable is defined as the bus of the system. The signal travels through all stations. Each station checks the address of the signal and all stations that this signal passes along the way process the signal whether this address is relevant to them or not.
Advantages
- The cable structure is reliable.
- Adding a new station is easy.
- No central unit is needed.
Disadvantages
- Failure of one station disables the entire network.
- Fault detection is difficult
Ring:
A ring topology is a bus topology in a closed loop. Each station is an element of a ring and the information formed in the ring reaches all stations. Each station receives the information generated in the ring and the destination address. It accepts if the destination address is its own address. Otherwise, the incoming information will be out of the process. The information flow in the ring is unidirectional. In other words, the computers included in the ring are responsible for transmitting the incoming information. However, many ring networks today use two rings and obtain bidirectional information flow. No termination is required.
Advantages
- All devices on the network have the same privileges
- New devices added to the network have minimal impact on performance
- Does not need any server
Disadvantages
- Failure of one device on the network means the entire network crashes
- It is quite expensive as the amount of cable used is large.
Star:
Each device on the network is connected to router equipment such as a switch or hub with regulation capability in the center. The information sent from one station to the other first arrives at this central unit, and from there it is directed to the target.
Advantages
- Adding new devices to the network and removing existing devices is quite simple,
- Its structure and understanding are quite simple,
- In the Bus-Topology, only one device can send data at a certain time, while in the Star-Topology, more than one device can send and receive data on the line at the same time,
- Failure of a device on the network does not affect the data flow on the network,
- Detection of cable errors that may occur on the network is very simple.
Disadvantages
- Failure of the Switch / Hub in the center means the collapse of the network,
- Cable usage is quite high compared to other topologies.
Mesh:
In a mesh network topology, each device is connected to all other devices in the network via a dedicated point-to-point connection. Dedicated means that the connection carries data for only two connected devices. Let’s say we have n devices in the network, then each device must be connected to (n-1) devices in the network. The number of connections in a mesh topology of N devices will be (n * (n-1)) / 2.
Advantages
- There is no data traffic issue as there is a private connection between the two devices which means the connection is only available for these two devices. So this connection is secure.
- Mesh topology is reliable and robust. Because the failure of a link never affects other links and communication between other devices on the network.
- The mesh topology is secure because there is a point-to-point connection and therefore unauthorized access is never possible.
- Fault detection is quite easy in this topology.
Disadvantages
- The amount of cable required to create and connect the topology can get very tedious.
- The number of I/O ports required is very large as each device must be connected to other devices.
- There is a scalability issue. Because each device on the network has a private point-to-point connection. Therefore, it is not possible to send data to many devices at the same time.










